Reverse Engineering
Our efforts in Reverse engineering aids in identifying vulnerabilities, understanding threats, and formulating robust defense mechanisms, making it integral to maintaining a secure and resilient digital environment.
Our efforts in Reverse engineering aids in identifying vulnerabilities, understanding threats, and formulating robust defense mechanisms, making it integral to maintaining a secure and resilient digital environment.
Our focus in malware research involves dissecting and understanding the operation of malicious software. By documenting their behavior and impact, we provide crucial insights that aid in devising effective defensive strategies, contributing to a better understanding and stronger defense against emerging cyber threats.
We offer penetration testing services, identifying vulnerabilities by simulating real-world attacks on your digital infrastructure. Our process uncovers potential threats, providing actionable insights for improved security measures, ensuring robust defense and resilience for your business operations.
Our involvement in open-source focuses on offensive security techniques and tools. We utilize and contribute to community-driven projects. This collaborative approach promotes innovative solutions, ultimately strengthening defense against evolving cyber threats.

Malware Museum: Showcasing the Most Impactful Malware from the 1990s to the Early 2000s. Get Ready to Journey Back to the Golden Age of Malware.
More
Complete and Optimized Remote Desktop Application Entirely Coded in PowerShell (Multi-Screen, Keyboard Sync, Mouse Sync, Clipboard Sync, and More)
More
Comprehensive C# Project to Understand the Concept of Malware Command and Control (C2) Using FTP as a Communication Channel.
More
Medium Account Showcasing Our High-Quality Articles focusing on Malware Research, General Information Security and Programming.
More
Comprehensive Search Engine for Malware Evasion Techniques (Documentation, Code Snippets, YARA Rules, and More)
More
Secure remote desktop application for Microsoft Windows entirely written in PowerShell for the server and a cross-platform client.
More
Open-Source Application for Comprehensive Search and Exploration of Windows DLL Exported Functions for Malware Research and Analysis.
More
GitHub Profile Showcasing Our Open-Source Projects, Proof of Concept (POCs) and Snippets related to Malware and Offensive Security.
More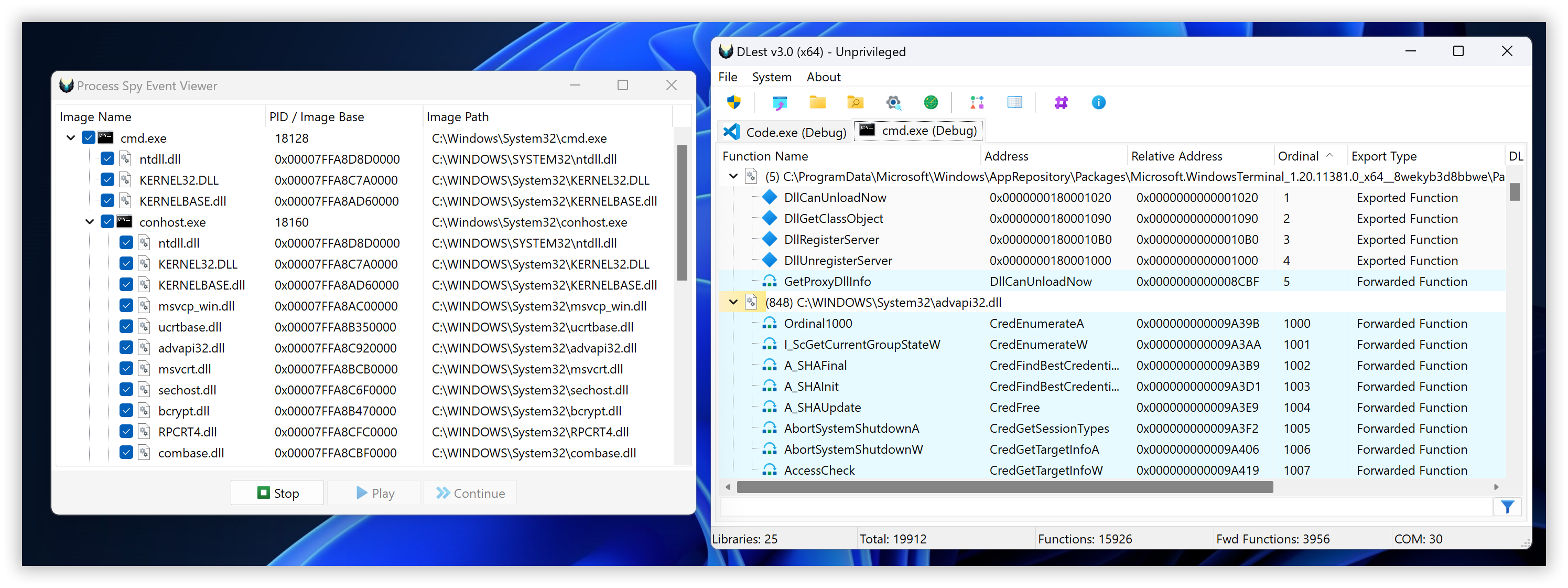
We are excited to announce the release of DLest v3.0! This major update brings a host of performance enhancements, user interface improvements, and powerful new features including:
Process Spy: Debug processes to monitor DLL Load events in real-time. File Hash Tools: Easily generate and compare file hashes. Enumeration of Lone Ordinals: Identify and analyze anonymous functions with improved accuracy. Enhanced Filtering System: Experience a more robust and intuitive export filtering system.
1 year ago

In this second article, we demonstrates how malware authors exploit Microsoft Windows application resources as malicious vectors to either store their dynamic configuration or additional payloads. The focus is on the Windows API, but it also details some aspects of the PE (Portable Executable) header, allowing for manual inspection and manipulation of resources.
1 year ago
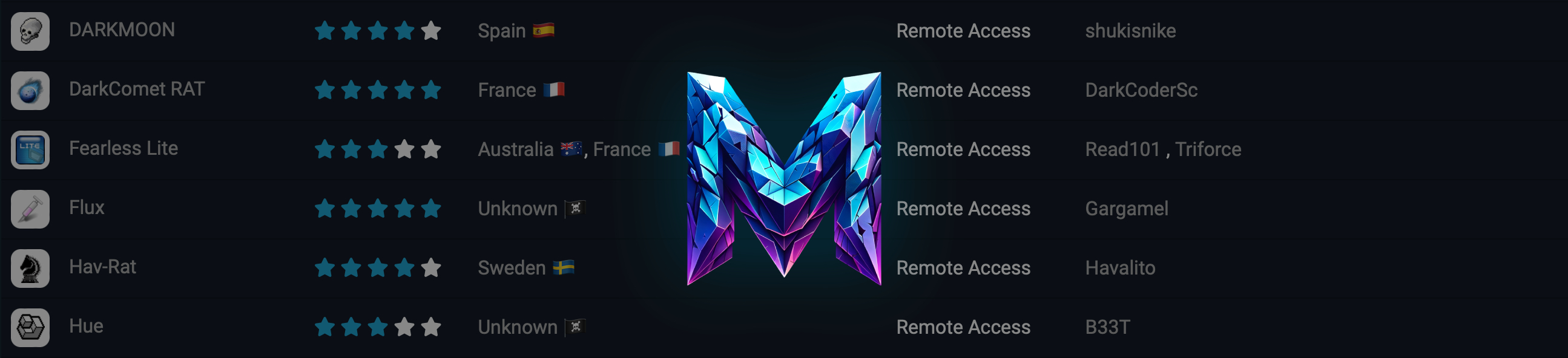
Welcome to the grand opening of Malware Gallery 1.0! We're excited to announce several new features that have been added since the beta version. One significant addition is the Archive mode, which expose a comprehensive database referencing over 10,000 malware and hack tool entries. This archive is compiled from a partial reconstruction of Mega Security's data spanning from 1998 to 2010.
But that's not all! We're dedicated to continuously updating our collection with new families and releases. Stay in the loop by subscribing to our RSS feed or following us on our social media channels to ensure you never miss a single update.
1 year, 2 months ago

In this new series of articles, we're looking at how malware authors deal with spreading their work, especially when they keep the source code secret. Malware configuration is key because it lets its malicious users to change settings to suit their needs. The first article will focus on a method called EOF, also known as PE Overlay, to show how it's used to store and read malware configuration.
1 year, 4 months ago
A new Unprotect evasion technique has been added, showcasing a sophisticated evasion technique named FuncIn with a working open-source demo. In short, FuncIn employs a payload staging strategy, diverging from the conventional method where all malicious functionalities are embedded within the malware file or stored in a third-party file/network location, such as a web server. Rather, with FuncIn, these functionalities are transmitted over the network selectively, triggered by the Command and Control (C2) server as needed.
1 year, 6 months ago
Here is a short example demonstrating the reflective loading of a Dynamic Link Library (DLL) into memory, whether sourced from disk or memory (supporting streams). This approach supports both 32-bit (PE) and 64-bit (PE+) DLLs. The technique enables the loading of exported functions either by their ordinal value or by the exported function name.
1 year, 6 months ago

In this latest installment of our "Malware Retrospective" series, we shift our lens to PrjRAPTOR, a lesser-known Remote Access Trojan that made its mark around 2008-2009, closing out the golden era of Trojan development before the focus shifted to profit-driven cybercrime. Our exclusive interview with its creator, "Ryan," provides invaluable insights into the Trojan's unique interface, development, and impact on the scene. This exploration offers a rare chance to connect with key figures who laid the groundwork for modern malware, enriching our understanding of this intricate landscape.
1 year, 9 months ago
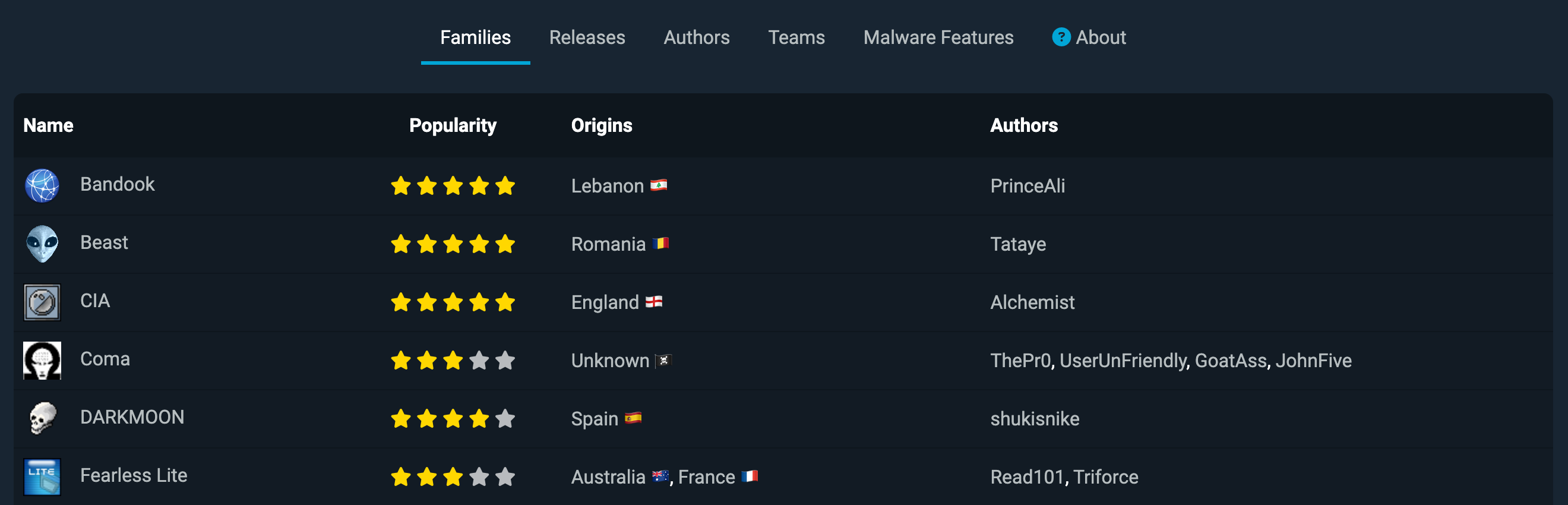
Introducing "The Malware Gallery" - Your interactive, living museum showcasing the most notorious trojans and malware from past decades. Now in its beta phase, this ever-evolving collection is set to expand, so stay tuned for updates!
There are two primary motivations behind the project: First, it serves as a homage to the ingenious, albeit malicious, software creations that inspired many of us, myself included, to pursue a career in cybersecurity. These "pieces of art" so to speak, have played a pivotal role in shaping the trajectory of my professional life.
Second, it's an educational resource for newcomers to the field. Understanding the history of malware is essential for comprehending the complexities of today's cybersecurity landscape. For those who didn't grow up exposed to these early examples, The Malware Gallery offers a rare glimpse into the origins of cyber threats, enriching your knowledge.
Additionally, this project complements my recent article series, "Malware Retrospective" adding a layer of depth and reciprocity to the topics covered.
1 year, 9 months ago

We are pleased to announce that our latest tool, SharpShellPipe, has been featured in Bad Sector Labs Blog's Last Week in Security (LWiS).
1 year, 9 months ago
New technique added: "Named Pipes / SMB," featuring two code snippets for demonstration purposes. The first snippet uses .NET (C#) to showcase Named Pipes usage, while the second employs WinAPI with Delphi. Both examples aim to illustrate the application of Named Pipes in different programming environments.
1 year, 9 months ago
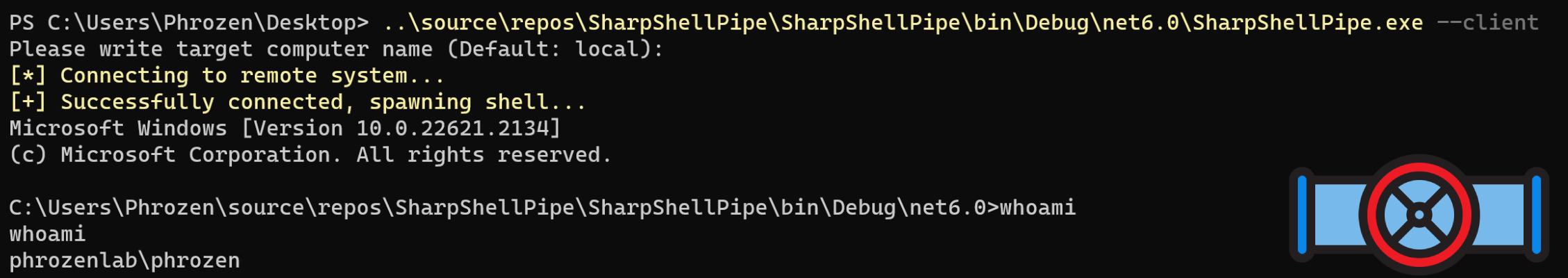
This lightweight C# application serves as a demonstration of how simple it is to interactively access a remote system's shell via named pipes using the SMB protocol. It includes an optional encryption layer leveraging AES GCM, utilizing a shared passphrase between both the server and the client.
1 year, 9 months ago
New evasion technique and snippet added for file extension manipulation using the Right-to-Left Override (RLO) character (U+202E). Malicious actors exploit this Unicode control character in file names to alter the visual display of extensions, making dangerous executables appear harmless to users. For example, invoice.pdf becomes invoiceexe.pdf by strategically placing the RLO character. This deception aims to trick users into unwittingly executing potentially harmful files.
1 year, 10 months ago

Continuing our enlightening "Malware Retrospective" series, we delve back into the depths of cybersecurity history. Following our thorough examination of Beast RAT, the early 2000s' formidable malware, we now turn our focus to another significant entity of that period, SubSeven. Conceived by the mysterious figure, Mobman, this Remote Access Trojan, also known as Sub7, remains an iconic marker in the evolution of digital threats. Join us as we explore its intriguing chronicles, offering both a retrospective glance and vital lessons for today's cybersecurity landscape.
1 year, 10 months ago
Attached please find the slides from my presentation on the Unprotect Project, delivered yesterday at the inaugural HackTheBox Meetup France, hosted by the ESGI School in Paris.
If you have any questions or need further clarification on any aspect of the presentation, please feel free to reach out.
1 year, 11 months ago
The release of version "3.0 Final" signifies the culmination of this project. I will not be adding any further features; the objective of this PoC was to demonstrate the creation of a reliable and secure C2 utilizing FTP(S). You're encouraged to develop your own version with tailored functionalities. As an exercise, you might consider implementing multi-threading tasking to prevent the application from hanging during long-duration tasks.
I will, however, continue to provide support for the project in terms of addressing potential bugs or opportunities for optimization.
1 year, 11 months ago
1 year, 11 months ago
1 year, 11 months ago
Support for encryption has been introduced, utilizing RSA and AES-GCM 256-bit algorithms, to safeguard the integrity and confidentiality of communications between agents and the C2 server.
1 year, 11 months ago
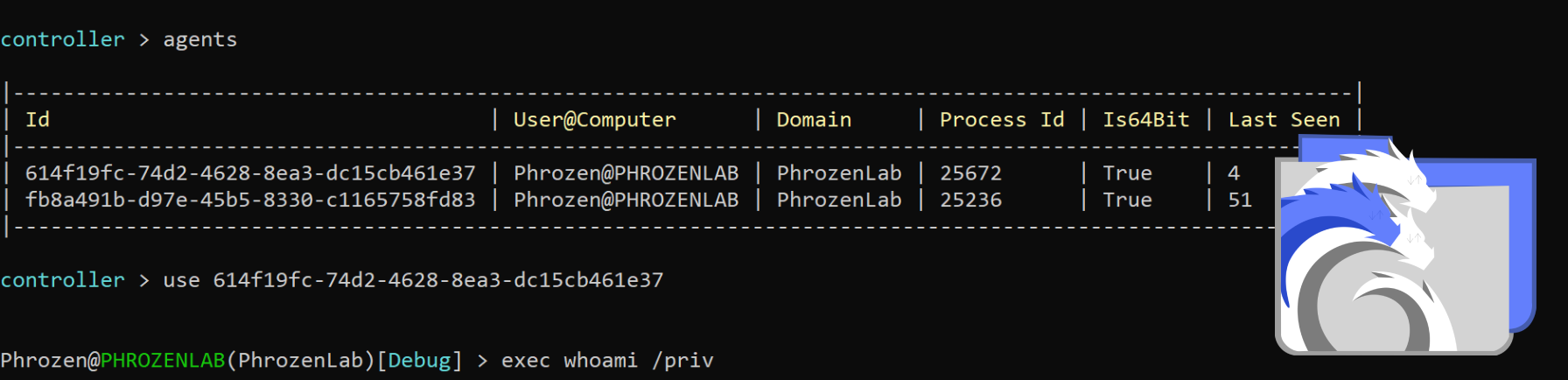
SharpFtpC2 is a small, experimental project aimed at exploring the possibility of using FTP(S) for relaying commands and responses between two remote computers. It employs the FTP protocol as a makeshift tunnel through which the computers, both acting as clients connected to an FTP server, can communicate. A simple session management scheme is used to keep track of the exchange of requests and responses.
2 years ago
An alternative version of the code snippet, crafted in Delphi, has been introduced for the "C2 via FTP(S)" technique. This variant expertly demonstrates the employment of the Windows API's from Windows Internet (WinInet) library.
2 years ago